Secure Remote Access Solutions
Enable your remote workers to securely access IT resources without sacrificing end-user experience and performance

Enable your remote workers to securely access IT resources without sacrificing end-user experience and performance

Secure remote access refers to multiple security modules brought together under a single solution. With remote access security, you can control which users access your resources, their permission levels and methods of authenticating their identity
Secure Remote Access is a comprehensive security solution which can typically include modules such as:
Zero trust network access: provides secure remote access solutions to applications and services based on defined access control policies.
Multi-factor authentication (MFA): in addition to a password, users must also provide an additional piece of evidence, such as a registered device or biometric.
Role-based access controls:only workers with specific roles can remotely access resources relevant for their jobs.
Single sign-on (SSO): users only need to input their password once per remote access session, even when switching between applications. This lowers the risk of typing in passwords on malicious portals.
Virtual Private Network: creates an encrypted tunnel between an end-user and a business resource to secure traffic on unprotected channels such as the public internet.
Having a Secure Remote Access Solution in place will help you reduce the risks associated with having workers connect to IT resources over high-risk connections, such as the public internet. If companies employ bring-your-own-device (BYOD) policies and the employees’ devices are not centrally managed, the exposure risk increases.
The transition to remote working initiated by the pandemic lockdowns has also brought a 400% surge in cyberattacks compared to pre-pandemic levels, as most businesses did not have adequate remote access security policies in place.
A holistic approach to providing Secure Remote Access capabilities is to integrate the security features into a wider Cloud Desktop solution. A Cloud Desktop hosts applications and data onto a cloud-based server which can be accessed by users through a web browser.
CloudSourceUSA solution has helped organizations improve their security posture by providing remote access features such as:
By design, Cloud Desktops deliver secure access benefits to support remote working. These include:
Off-device data storage: in a Cloud Desktop solution, all data is stored in the Cloud and does not reside on the end-user device. In the event that the device is compromised, the data will not be affected.
Centralized management: by using Cloud Desktop as your secure remote access solution, a central IT function creates and manages user accounts, providing and revoking access to relevant resources and enforcing policies for groups of users.
Daily Backups: CloudSourceUSA performs daily backups of your Cloud data, such that in the event of a failure, you can simply revert to a safe copy.
End-to-end encryption: in a Cloud Desktop solution, communication between user devices and cloud resources are fully encrypted, meaning that nobody without authorization is able to access any information

CloudSourceUSA’s turnkey solutions include comprehensive Secure Remote Access technologies to enable remote working with peace of mind.
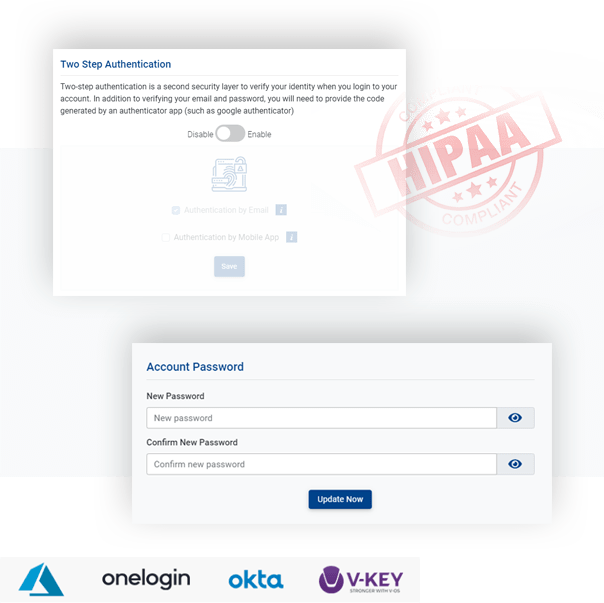
You can enforce Multi-factor authentication for your users for added security, requiring users to provide a biometric pass such as a fingerprint, or a device token such as a mobile phone.
CloudSourceUSA integrates with your preferred SSO provider such as Azure SSO, OneLogin, Okta, Google SSO, V-KEY or any other SAML compatible SSO provider. Users can securely authenticate remote access sessions with multiple applications and websites by using just one set of credentials.

Employees can securely connect from remote locations to cloud resources even when using the public internet.
CloudSourceUSA can integrate with cloud-based or on-premise Active Directory for identity and access management service.
Even in the event of a ransomware attack, V2Cloud protects your resources with daily snapshots retained offline for a complete ransomware protection.